Cyber Library
Turn one‑and‑done training into real behavior change with relatable, bite‑sized content that protects your people at work and at home.
library
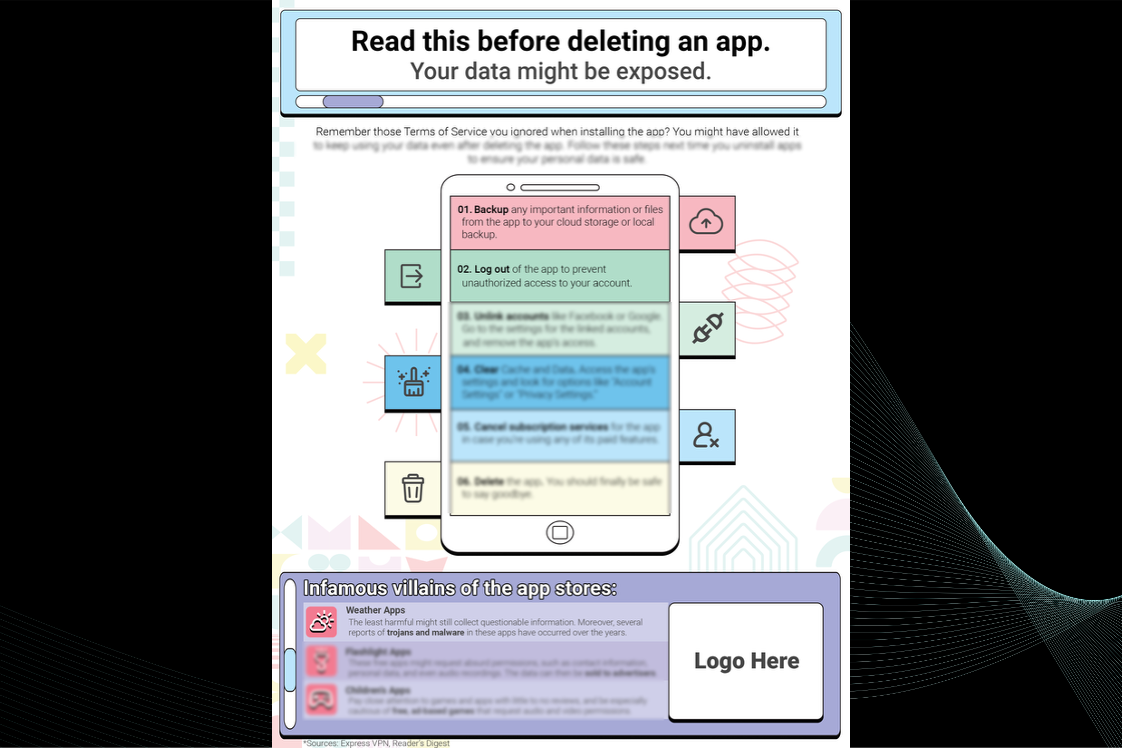
Stop! Follow This Checklist Before Deleting Any App
Description
Follow This Checklist Before Deleting Apps – Protect Your Data First
Deleting an app doesn’t mean your data disappears with it. The Stop! Follow This Checklist Before Deleting Any App infographic walks users through six critical steps to ensure personal information is fully protected before hitting “uninstall.” From backing up important files to unlinking connected accounts, this visual guide helps prevent leftover data from falling into the wrong hands. It also highlights three types of apps most likely to put your security at risk—making it a must-read for employees, students, and families looking to improve their cyber hygiene.Ideas for How to Use This Resource:
- Display in office break rooms, IT support desks, or tech help areas
- Include in new hire or student onboarding materials
- Post to your company intranet, LMS, or digital resource library
- Share during Cybersecurity Awareness Month or device clean-up campaigns
- Distribute as a take-home tip sheet for employees’ families
$149.00
Attributes
- Includes your animated logo.
- Standard EULA
Pay With:

Features
Branded for you
Your company logo is included in all content
Quick Delivery
Receive your branded resource in less than 48 hours
Easy to Implement
Quick and easy distribution to your platforms.
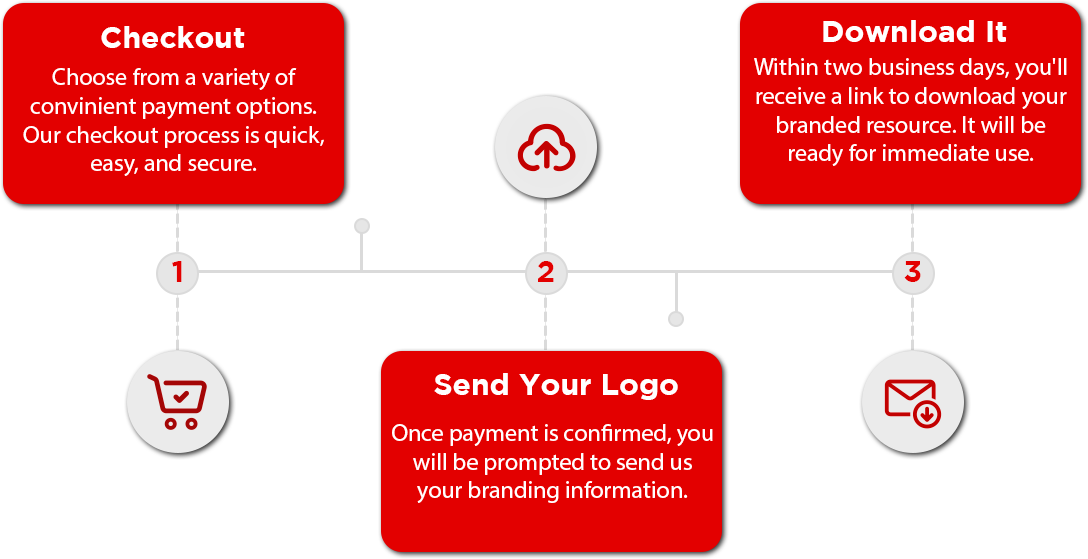
3-Step Delivery Process
Receiving your branded resource is quick and easy.
During the checkout process, you will be prompted to upload your logo or send it via email. Once we have your brand material, we will deliver this resource branded for your organization in less than 48 hours. It will arrive via the e-mail you provided.
You Might Also Like
$49.00
This poster, customized with your company logo, is part of our “Who’s Hacking Me?” series, focusing on fraudulent bank account alerts and serving as a valuable tool for ongoing education on phishing and deceptive email practices. Print and/or send online.
$149.00
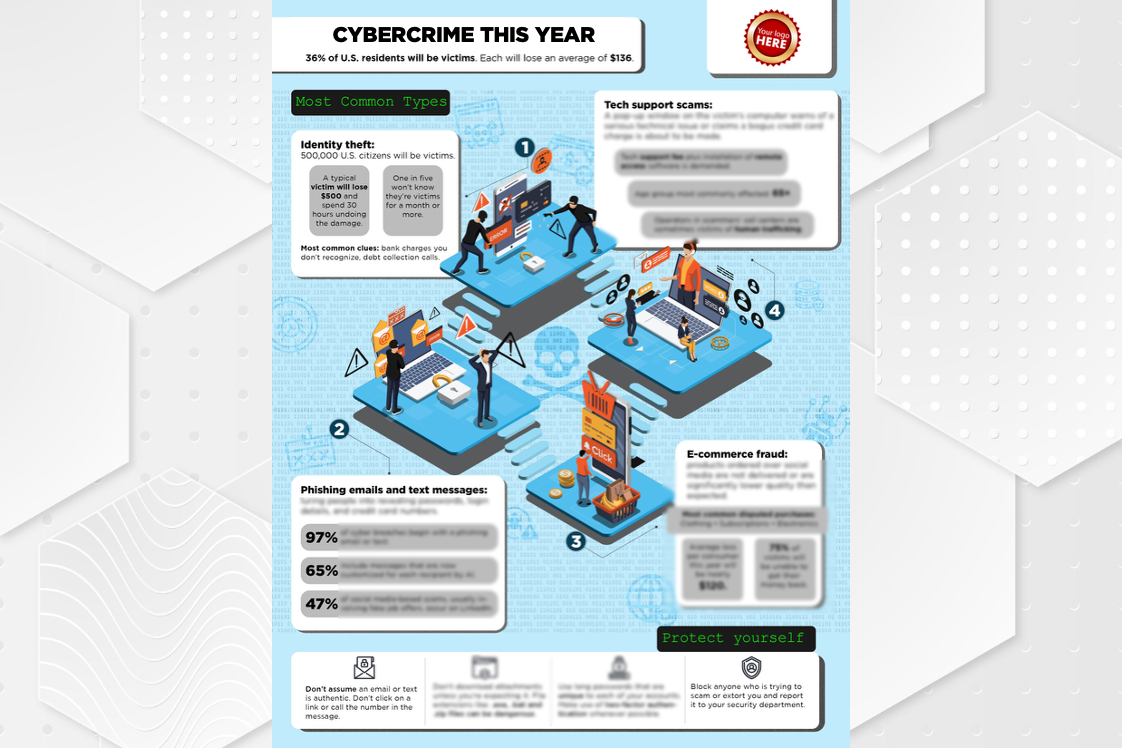
An eye-catching infographic on the top cyber crimes of 2024 with simple tips to stay safe at work and at home.
$249.00
Chatbots are the fastest-growing consumer app in history, part of artificial intelligence. This video explains what chatbots are, how they work, and why we need to be not only amazed, but careful.