Cyber Library
Turn one‑and‑done training into real behavior change with relatable, bite‑sized content that protects your people at work and at home.
library
What to Do After a Big Breach
Description
From Breach Headlines to Personal Action—Train Smarter with Real-World Scenarios
The What to Do After a Data Breach quiz is a live-scoring, 5-question interactive tool that teaches employees and their families how to respond effectively to the most common and high-profile data breach situations. Built around real incidents—including the “mother of all cyber breaches,” the Microsoft executive email hack, and retail and mortgage company exposures—this quiz transforms headlines into teachable moments, giving users a clear roadmap for protecting themselves in the aftermath of a cyber event.Key Features and Topics
-
- Real breach scenarios involving companies like Microsoft, North Face, LinkedIn, LoanDepot, and social media platforms
- Key response actions after receiving suspicious messages or breach alerts
- Understanding how threat actors bypass security using phishing and token compromise
- Tips for securing accounts with MFA, unique passwords, and credit monitoring
- Action-focused feedback after each question with live scoring
Ideas for How to Use This Resource
- Post-Phishing Simulation Training
- Cybersecurity Incident Response Follow-Up
- Employee Newsletters or Family Outreach
- LMS or Intranet Security Module, Quarterly Awareness Campaigns
- Password Management Campaigns
$149.00
Attributes
- Includes your animated logo.
- Standard EULA
Pay With:

Features
Branded for you
Your company logo is included in all content
Quick Delivery
Receive your branded resource in less than 48 hours
Easy to Implement
Quick and easy distribution to your platforms.
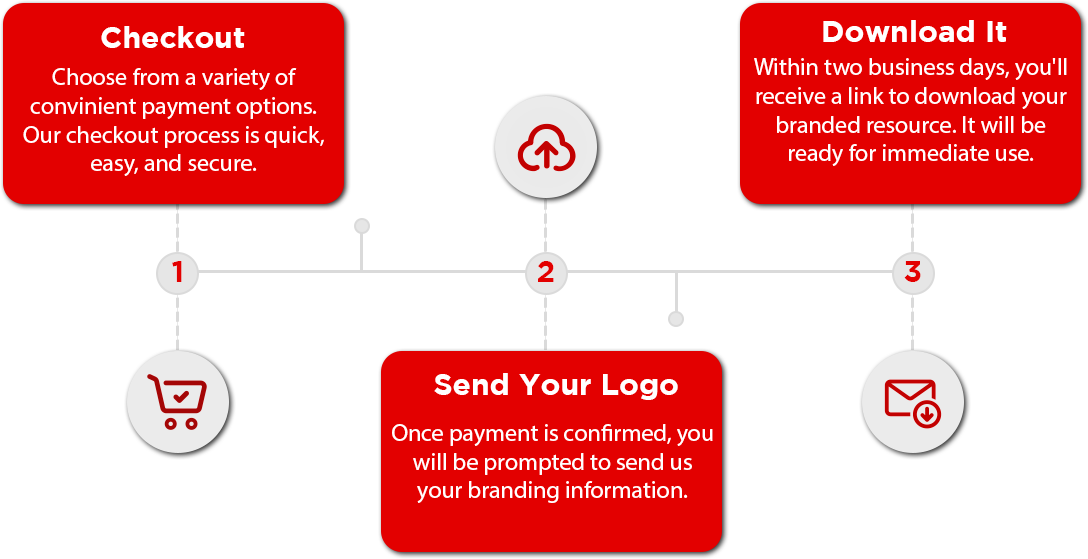
3-Step Delivery Process
Receiving your branded resource is quick and easy.
During the checkout process, you will be prompted to upload your logo or send it via email. Once we have your brand material, we will deliver this resource branded for your organization in less than 48 hours. It will arrive via the e-mail you provided.
You Might Also Like
$49.00
The most common scams at tax time include signs that an official-looking email or text communication is bogus.
$249.00
A short, powerful video that helps parents understand how oversharing about their kids online can lead to scams and identity theft—and what to do instead.
$75.00
It catches even the most suspicious victim: a text or email that includes seemingly accurate details about an overdue tax bill.