BrowserGate: Is Microsoft Running One of the Largest Corporate SpyOps Ever?
blog
A major digital privacy scandal, dubbed “BrowserGate,” has surfaced, alleging that LinkedIn is conducting massive, covert surveillance on its users.
. The investigation was spearheaded by Fairlinked e.V., a German association representing commercial LinkedIn users and toolmakers.
. They discovered that every time a user visits LinkedIn, hidden scripts interrogate the user’s browser to see which other software they have installed.
Table of Contents
What’s Actually Happening Behind the Scenes?
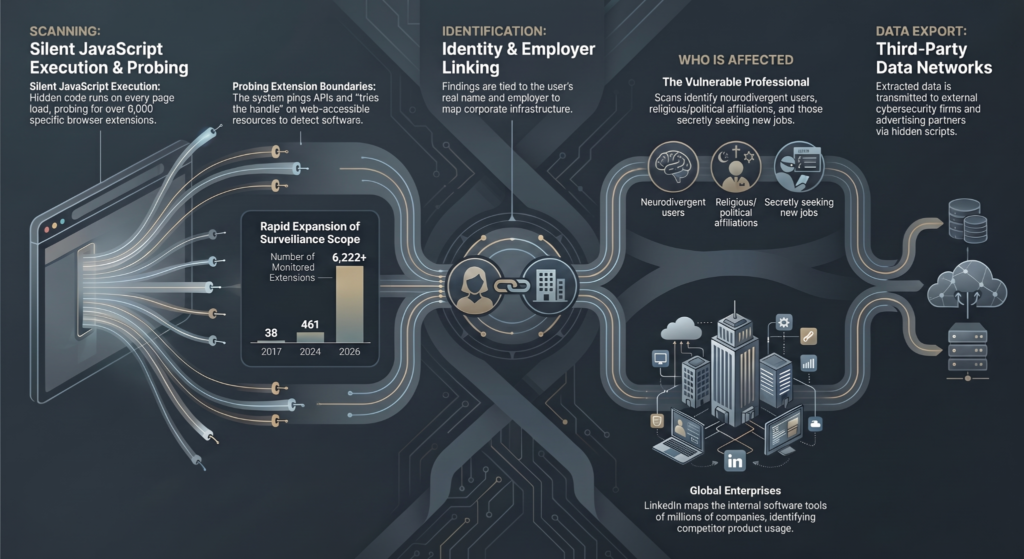
According to investigations, when any of its 1 billion users visits the site, LinkedIn deploys hidden scripts that run whenever a page loads.
These scripts reportedly:
- Scan for over 6,200 browser extensions
- Attempt to communicate directly with those extensions
- Collect and transmit that data back to LinkedIn—and third parties, including the American-Israeli cybersecurity firm HUMAN Security (formerly PerimeterX) and Google
No pop-up. No warning. No meaningful consent.
Why This Isn’t “Just Another Tracking Pixel”
Most tracking is anonymous. This is not.
LinkedIn operates on real identities—your name, job title, and company.
That changes everything.
1. Your Personal Life, Inferred
Installed extensions can expose:
Political Opinions
Religious Beliefs
Disabilities
Not because you shared it—but because your tools did.
2. Job Hunting—Exposed
LinkedIn allegedly scans for job search tools.
Translation:
You could be flagged as “open to leaving”… before you ever say a word.
3. Competitive Intelligence at Scale
By detecting tools like Apollo or ZoomInfo, LinkedIn could:
- Map which companies use which platforms
- Identify competitors’ customers
- Gain an unfair strategic advantage
That’s not marketing insight. That’s surveillance with business implications.
The Legal Storm Is Already Here
Two class-action lawsuits are now underway in California, accusing LinkedIn of violating:
- The Electronic Communications Privacy Act
- State-level computer fraud laws
LinkedIn’s response?
They’ve dismissed the claims as a “fabrication.”
Their defense hinges on:
- Disclosure: claiming users were informed via privacy policies
- Security: arguing that the scans prevent scraping and abuse
But critics aren’t convinced—especially given the scale and depth of the alleged data collection.
What This Means for Your Organization
This isn’t just a user privacy issue. It is a corporate risk issue.
If true, this kind of scanning could:
- Reveal your internal tech stack
- Expose employee behavior patterns
- Undermine competitive positioning
And most companies wouldn’t even know it’s happening.
How to Reduce Your Exposure (Right Now)
You don’t need to wait for the lawsuits to settle.
Start limiting your attack surface:
- Adopt privacy-first browsers
Brave and similar tools give tighter control over scripts, reducing exposure to Chrome-based extension probing - Use private sessions
Incognito mode can isolate extension access - Avoid default apps
Mobile browsers often provide more visibility and control than native apps - Block known scripts
Advanced teams can filter specific tracking components tied to this activity
The Bigger Picture: Visibility Is the Real Vulnerability
BrowserGate highlights a hard truth:
Most organizations invest heavily in endpoint security, firewalls, and awareness training while
overlooking what’s happening inside the browser.
Modern risk is quietly expanding on this frontier.
How Aware Force Helps You Close That Gap
At Aware Force, we turn complex, invisible threats like this into clear, actionable awareness for your teams.
Because security isn’t just about tools—it’s also about:
- Understanding real-world attack vectors
- Recognizing hidden data exposure
- Building behaviors that reduce risk at scale
If your employees don’t understand how platforms actually interact with their data, they can’t protect it.
Ready to Bring This Issue to Your Team’s Attention?
Let’s show your teams what’s really happening beneath the surface—and how to respond.
Get in touch with Aware Force to transform emerging threats into measurable awareness and smarter security behavior.
Sources: browsergate.eu, PCMag, Cybernews
Get the latest insights in cybersecurity. Subscribe to the Aware Force Cyber Blog
Insightful cyber news, fresh ideas for engaging your employees and more.
Search
Richard Warner is a recognized expert on human cyber risk and the founder/CEO of Aware Force, where he and his team create cybersecurity content tailored to each client’s culture that is engaging, relatable, and effective.
Leveraging his decades of experience as a prominent journalist and communicator with outlets including FOX and the GPB Television Network, Richard helps organizations worldwide transform human weak links into their strongest digital defense.
He is based in Atlanta and pioneers effective strategies for security culture and employee engagement.